Connect Kairro to the environments where AI work actually happens.
In Kairro, Integrations starts with managed browsers and endpoint collectors, then extends into notifications, SIEM, and downstream security tooling. The result is one operating layer from endpoint coverage through routed response.
Enterprise-Grade Integration Layer
Managed endpoint coverage first, then downstream routing for security, governance, and operations teams.
Browsers and collectors
Kairro manages the endpoints where AI activity and policy enforcement actually happen.
- Browsers — extension fleet, policy sync, command delivery, and posture.
- Collectors — workstation coverage, policy bundles, reviews, and health.
Findings, decisions, and telemetry
Unified payloads for AI interactions, investigations, and endpoint actions.
- AI events with allow / warn / block decisions
- DLP matches, severities, and snippets (redacted)
- Shadow AI detections and findings
- Collector reviews, command state, and operational health
Reliable and observable
Built-in health metrics, error tracking, and privacy-safe payloads for systems downstream of Kairro.
- Per-integration status and last error
- Channel-level delivery metrics
- Secrets masked by default
- Org-scoped configuration with zero cross-tenant bleed
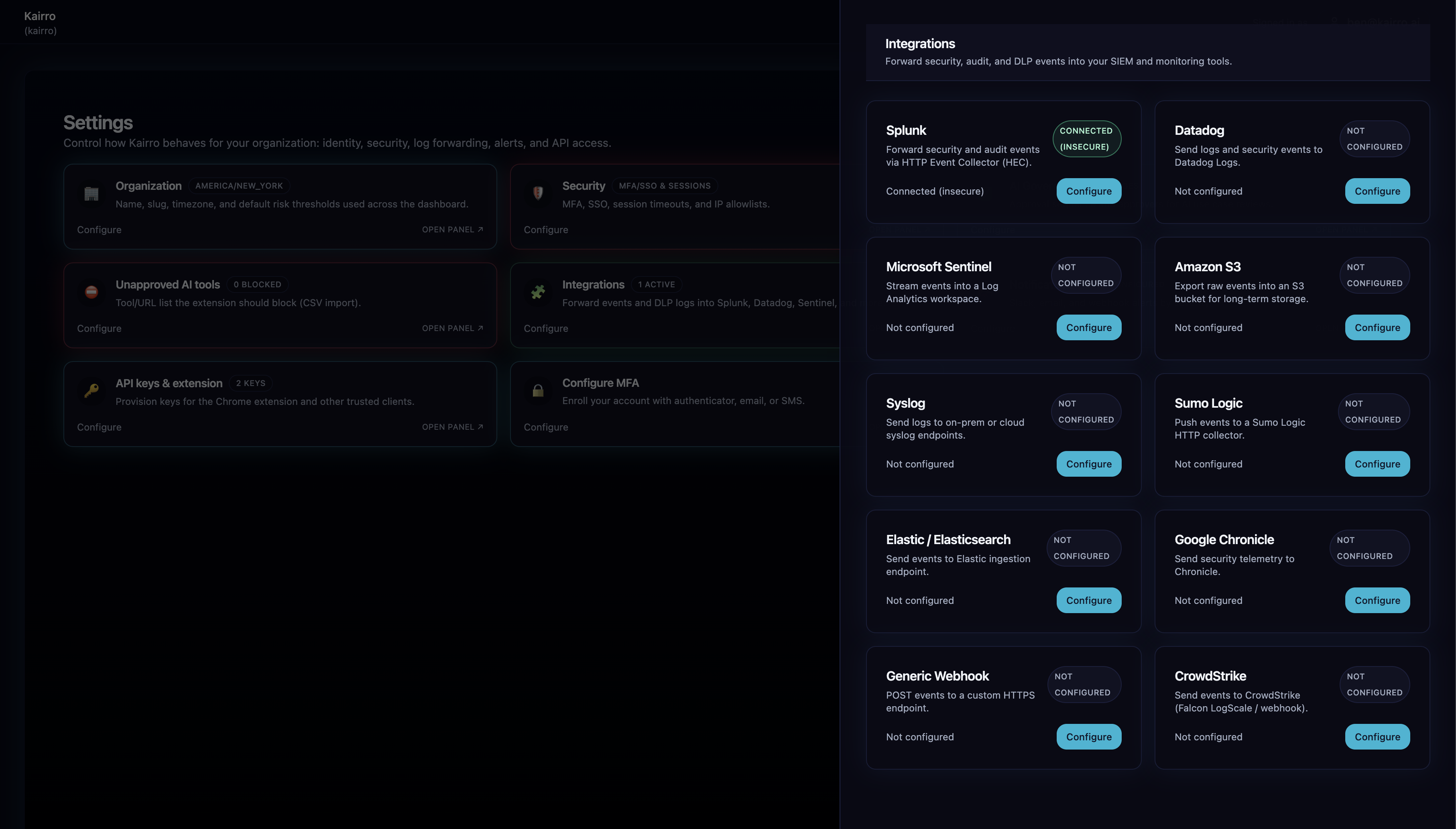
Outbound Integrations
Forward AI telemetry to SIEM, SOC, or analytics stacks with structured, privacy-safe payloads.
Built-in connectors
- Splunk HEC
- Datadog
- Sumo Logic
- Elastic / Elasticsearch
- Google Chronicle
- CrowdStrike (forward-compatible)
- Generic Webhook
Per-org settings: endpoint, auth/secret, custom fields, enable/disable, last status.
Structured JSON
- Event core: org, identity/user, aiTool, action, riskLevel, blockedReason, timestamp
- DLP summary: totalMatches, maxSeverity, critical/high flags
- DLP matches: pattern name, severity, offsets, rule ID
- Metadata: extension ID, browser client, tokens, evaluation context
Observable delivery
- Per-integration status and lastError
- Delivery attempts tracked with soft-failure logging
- Partial/log-only delivery indicators
- Surfaced in Ops dashboard for quick troubleshooting
Notification Channels
Route alerts to the right teams through a configurable notification matrix.
Collaboration & incident
- Slack
- Email (SMTP)
- Microsoft Teams
- PagerDuty
- Opsgenie
- Webhook
Recipient lists, severity routing, templates, per-channel toggles.
Context-aware routing
- Evaluates event risk, DLP severity, Shadow AI severity
- Considers policy action (warn/block) and org risk thresholds
- Creates Notification records and Delivery attempts
- Logs outcomes for auditability
Notifications matrix
Configure which events trigger alerts, severities per channel, and test each channel from the console.
- Slack/Teams webhooks, SMTP settings
- Severity matrix updates and recipient management
- Masked secrets in UI and API responses
Ops & Health Monitoring
Surface delivery reliability, errors, and channel health directly in the Ops dashboard.
Integration health
Observe delivery reliability across every provider.
- 24hDelivery success rate by provider
- ErrorsLast delivery error and status
- AuthConnection and authentication failures
- LatencyTimeout and latency statistics
Notification health
Track alert delivery quality across every channel.
- VolumeNotification counts per channel
- FailuresFailed delivery attempts by channel
- WebhooksSlack/Teams webhook failure visibility
- Email/IREmail and PagerDuty/Opsgenie error tracking
Security & Privacy
Privacy-safe by design: minimized payloads, encrypted secrets, and strict tenant isolation.
Encrypted at rest, masked in API responses, never re-shown after creation.
- EncryptSecrets stored with encryption
- MaskMasked by default in UI/API
Only what’s needed for investigation and auditability — nothing more.
- 256Prompt/response content truncated to 256 chars
- SnippetsDLP snippets stored with offsets, not full text
Strict tenant boundaries for configs, secrets, and payloads.
- TenantPer-org integration configurations
- No bleedNo cross-tenant sharing of data or secrets
Admin API & Configuration
Manage integrations and notification settings programmatically or through the console.
/v1/admin/integrations
/v1/admin/integrations/:id- CRUD operations and provider-specific test calls
- Enable/disable integrations
- View last error, status, and masked config
/v1/admin/notifications/config- Slack, Teams, email settings
- Severity matrix updates and recipients
- Channel test endpoints
- Secrets masked automatically
Example Use Cases
Real-world workflows across security, compliance, IT, and platform teams.
- Forward all DLP-critical events to SIEM
- Trigger PagerDuty for high-severity Shadow AI incidents
- Correlate AI use with network, identity, or endpoint telemetry
- Archive AI interactions into Splunk or Chronicle
- Maintain immutable logs for audits
- Prove compliance with regulatory requirements
- Notify Teams/Slack on policy changes
- Alert when employees use unapproved AI tools
- Inform owners when thresholds are breached
- Track AI adoption trends
- Monitor operational health
- Feed custom analytics pipelines
Why Kairro’s Integration Layer Is Different
Purpose-built for AI security with unified signals and first-class observability.
Includes AI tool, risk, DLP details, Shadow AI metadata — fields traditional systems lack.
Events, DLP, Shadow AI, and governance share one consistent pipeline.
Health metrics, delivery tracking, and surfaced errors keep teams confident.
Redacted, minimized, and encrypted data across outbound and notification paths.
The Result
Kairro becomes the AI security telemetry hub for your organization: your SOC gains visibility, compliance teams get audit-ready evidence, IT receives actionable alerts, SIEMs ingest normalized events, and governance stays measurable.